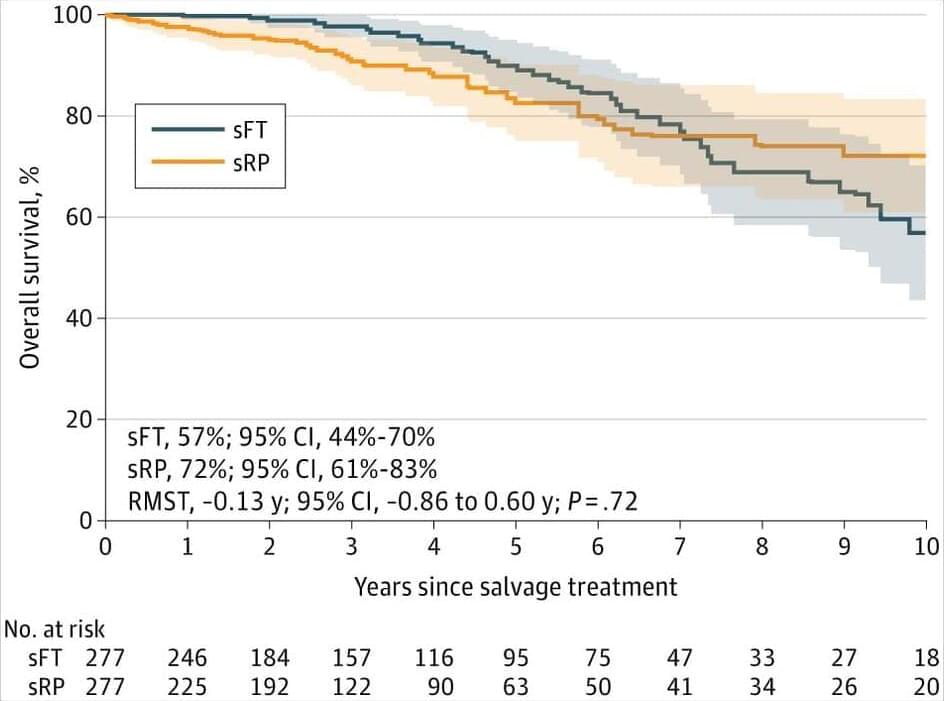
In localized radiorecurrent ProstateCancer, salvage focal therapy provided similar 10-year survival outcomes as radical prostatectomy but resulted in substantially fewer perioperative complications.
Question How do cancer control and perioperative complications compare after salvage focal therapy vs salvage radical prostatectomy for localized radiorecurrent prostate cancer?
Findings In this cohort study with a mean matched cohort size of 554 patients with biopsy-confirmed, localized recurrent prostate cancer, 10-year cancer-specific survival and overall survival were not meaningfully different between salvage focal therapy and salvage radical prostatectomy. The adjusted odds of any and major complications were approximately 24 and 9 times higher, respectively, following salvage radical prostatectomy.
Meaning Salvage focal therapy and salvage radical prostatectomy are both effective for treating localized radiorecurrent prostate cancer, though salvage focal therapy confers fewer perioperative complications.