Everyone is currently watching the major tech giants throw billions of dollars at the AI arms race, cheering for whichever foundation model happens to top the leaderboards this week.
It is an incredible spectacle to watch unfold, but focusing too closely on the tech itself might mean we are missing the actual business revolution happening right under our noses.
We have seen this exact economic shift before. The biggest winners of the internet era weren’t the ones who built the physical infrastructure or supplied the goods; they were the platforms that organized the supply and owned the user relationship. The same economic laws are now coming for artificial intelligence, actively turning “intelligence” into a basic, interchangeable utility.
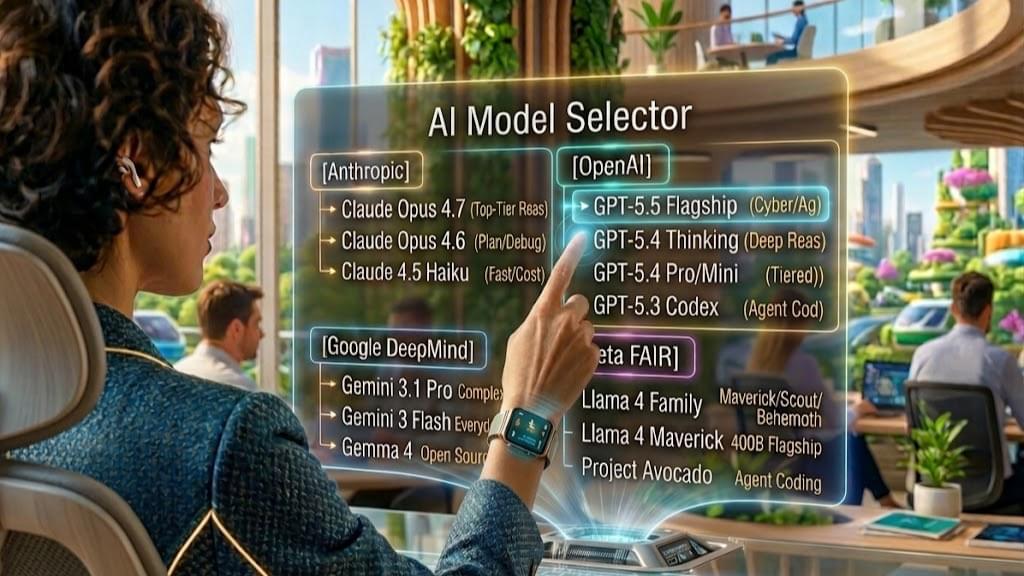
The real value moving forward is no longer in the models themselves, but in the seamless interfaces that aggregate them. If you want to protect your business from vendor lock-in and position your team for ultimate flexibility, it is time to rethink your approach.
Read my full blog post to dive into why the future of AI belongs to the aggregators, and how your business can strategically capitalize on this shift.
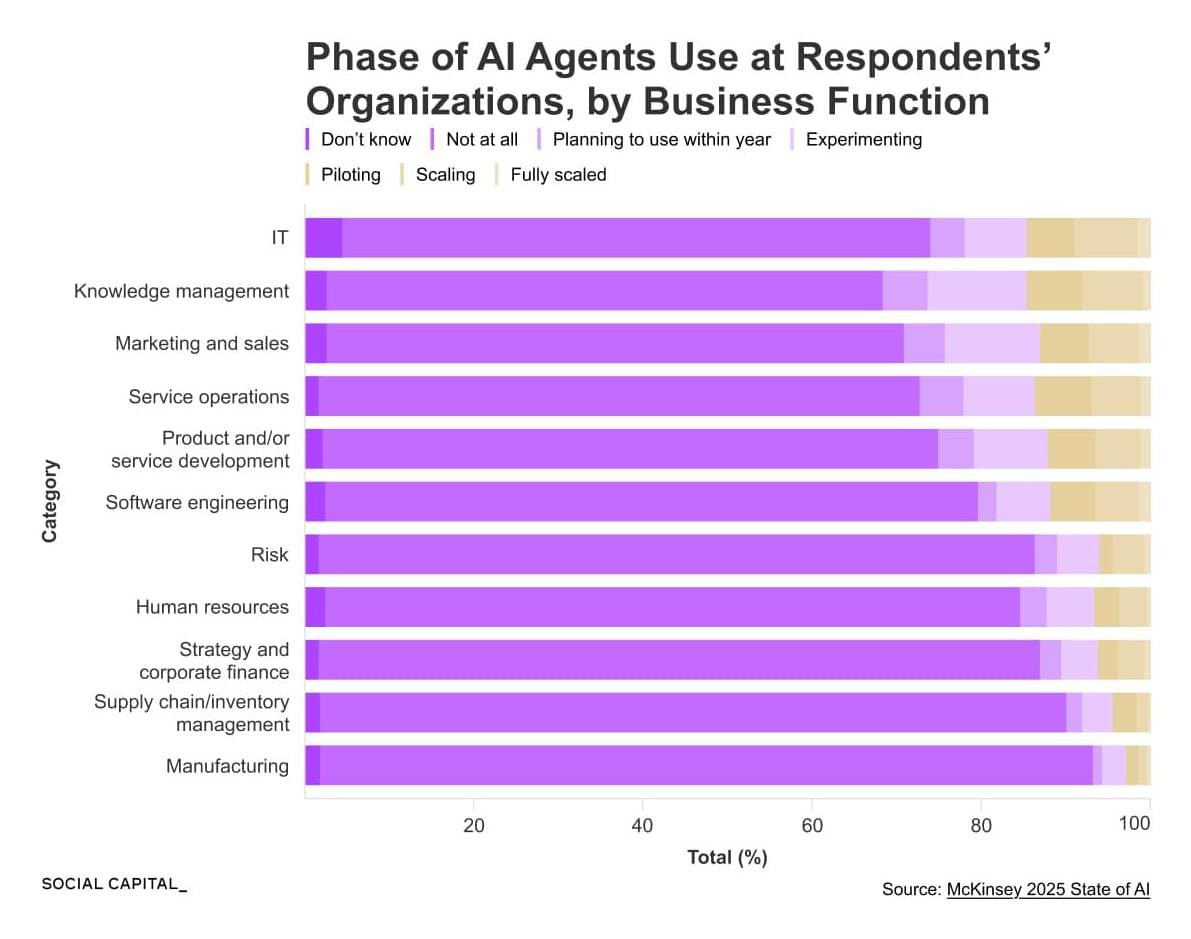
We spend an enormous amount of time obsessing over the titans of the AI arms race. Every single week seems to bring a breathless new headline about OpenAI, Google, Anthropic, or Meta releasing a foundation model that edges out the competition on some obscure benchmark test. We find ourselves endlessly arguing over parameter counts, context windows, and raw reasoning capabilities, captivated by a multi-billion-dollar war unfolding in real-time.