At age 49, Jan Janisch-Hanzlik’s multiple sclerosis was destroying her freedom to live the life she wanted. She gave up her active nursing job for a desk role. Frequent falls made her afraid to carry her grandchildren. She had to move to a bigger house to make room for the wheelchair she feared she might end up needing full-time.
Even the best available medication wasn’t improving Janisch-Hanzlik’s symptoms, and she worried they’d only get worse. So when she learned about a trial of CAR T cell therapy at the University of Nebraska Medical Center in Omaha, close to the city of Blair where she lives, she phoned the clinic every other month until they were ready to enroll her as the first patient.
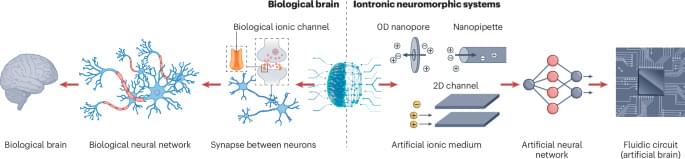
Originally designed to target and wipe out cancer by reprogramming the patient’s immune cells, CAR T is now being offered to patients in hundreds of clinical trials for autoimmune conditions like multiple sclerosis, lupus, Graves’ disease, vasculitis and many others. The hope is that CAR T can duplicate the success it has demonstrated in a range of blood cancers by hunting down and eliminating cells that target the self in autoimmune diseases. This would essentially reset the body’s defenses to a state like the one that existed before the disease took hold.