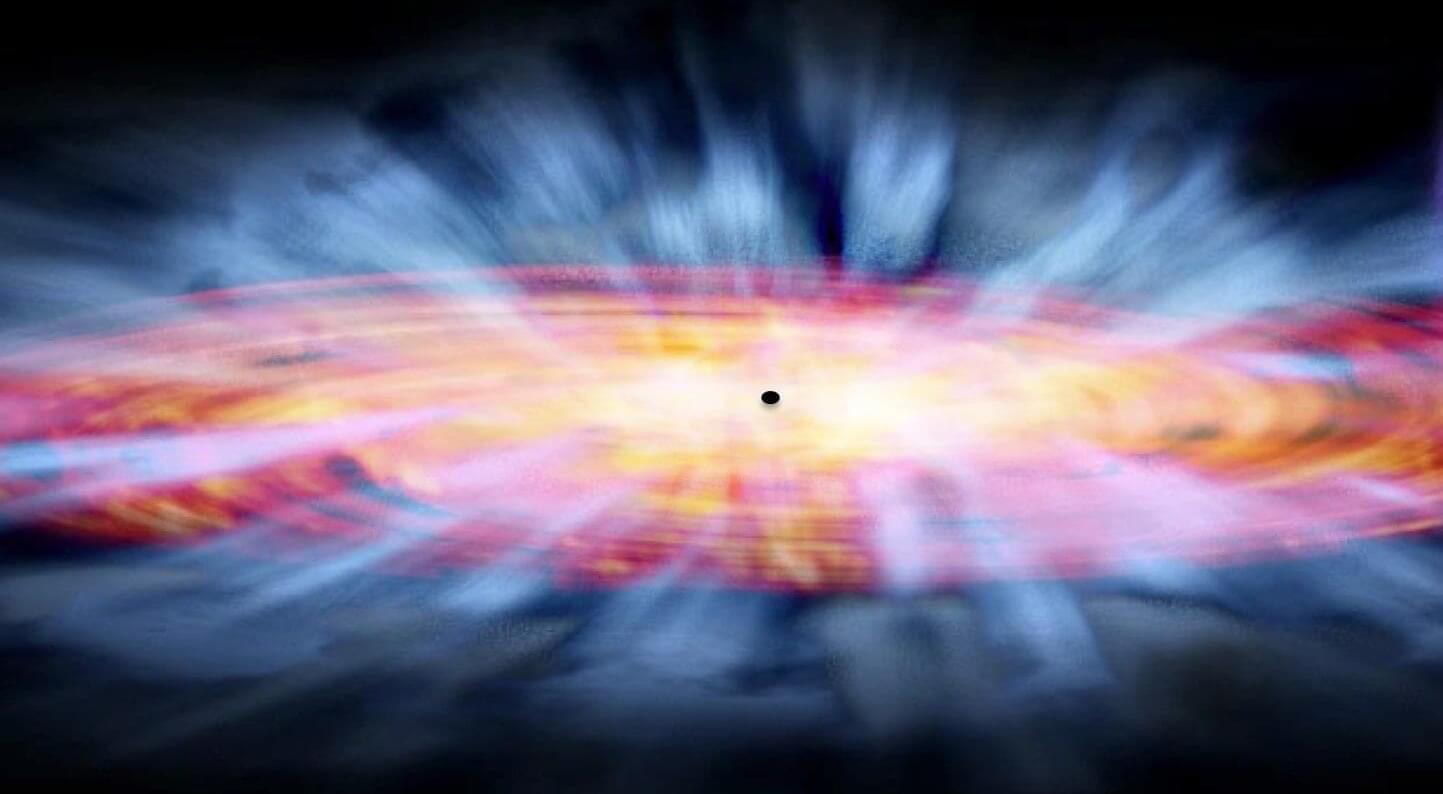
Gravitational waves are tiny ripples in spacetime. Their first direct detection in 2015 marked a revolutionary moment in astronomy. Today, we have a thorough understanding of signals that travel far from their sources through quiet, nearly empty space, such as those emitted when black holes merge. In this case, the wave can be considered a minor disturbance on a silent background. The distinction between “background” and “wave” is clear, and the quantity measured by the detector—a tiny stretching and squeezing—is clearly determined.
In cosmology, however, things are more subtle. The focus shifts to the universe in its entirety—encompassing spacetime and everything contained within it, such as stars, black holes and galaxies. The background itself is dynamic. Small fluctuations in density and velocity gently stir spacetime everywhere, blurring the boundary with the wave.
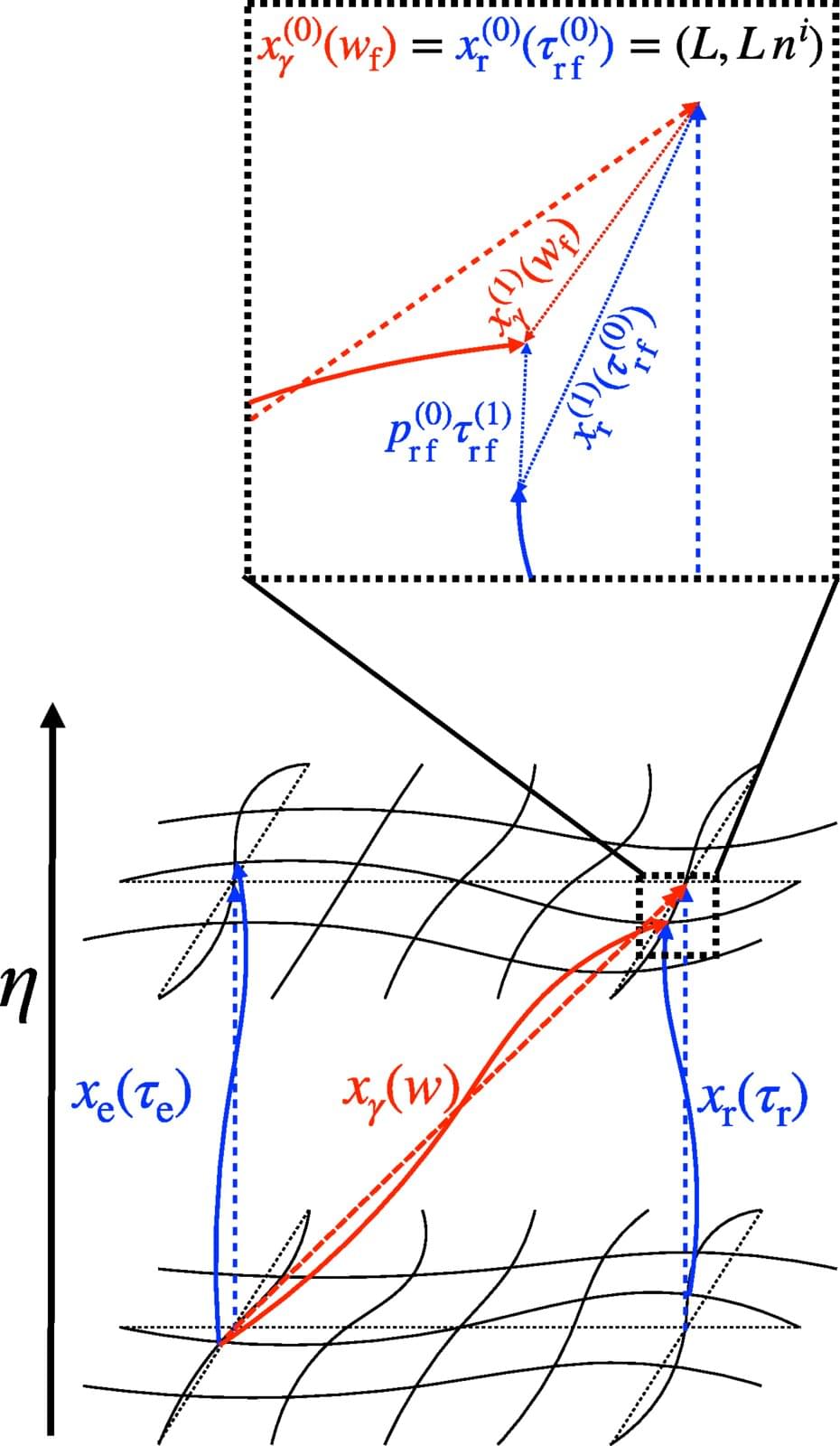
But what exactly does a gravitational-wave detector measure when the entire universe is gently vibrating? Previously, theoretical predictions were entirely dependent on the choice of mathematical coordinates. However, the only meaningful quantity is what a real instrument records, which must be coordinate-independent.