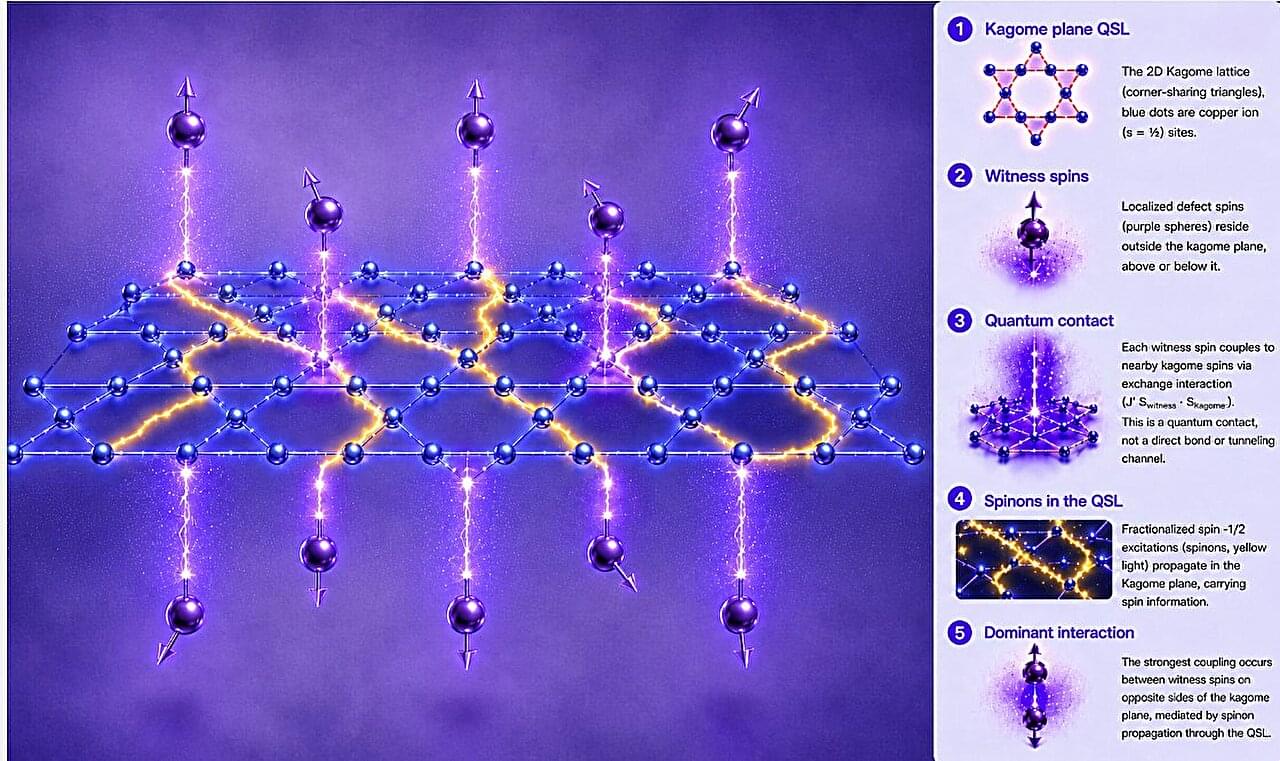
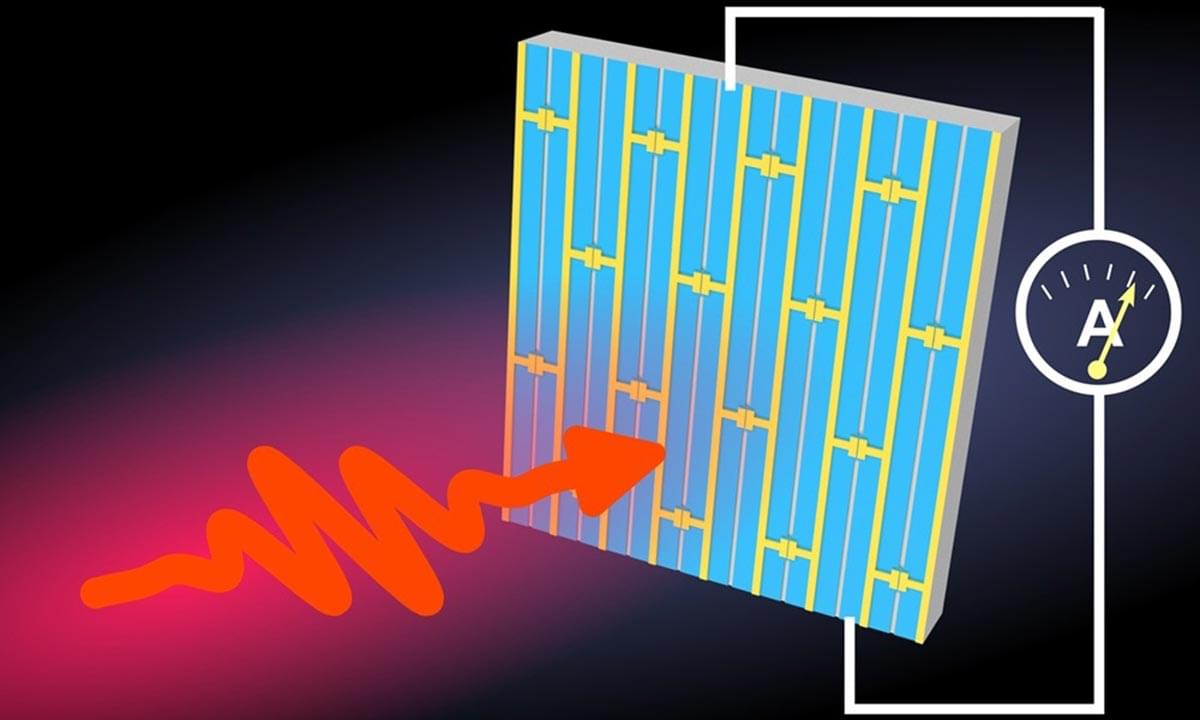
Quantum materials are a class of exotic materials with special properties that are governed by quantum mechanics rather than classical physics. Those properties—like superconductivity, entanglement and unusual forms of magnetism—often originate in the tiny repeating patterns of atoms inside crystals, but through clever engineering, they can be observed and controlled at a more human scale. Quantum materials are helping to power the quickly growing field of quantum computing and could find their way into future generations of energy-efficient electronics.
Designing new materials from the atomic scale up, however, requires intense modeling and simulation. Some materials may appear ordinary when viewed as small clusters of atoms, yet reveal new and useful properties when their atomic building blocks repeat and interact over larger distances. Researchers must be able to accurately predict behaviors at large scales in order to find materials with practical applications—otherwise, designing new materials is a slow and costly trial-and-error process.
In the past 50 years, supercomputers have helped materials scientists solve some of those thorny prediction problems, but two recent studies from the University of Washington demonstrate how newer computing techniques can help researchers sniff out promising quantum materials to pursue.