Government turns recommendations into requirements as crippling attacks rise



The U.S. Cybersecurity & Infrastructure Security Agency (CISA) is warning government agencies to patch an Oracle Identity Manager tracked as CVE-2025–61757 that has been exploited in attacks, potentially as a zero-day.
CVE-2025–61757 is a pre-authentication RCE vulnerability in Oracle Identity Manager, discovered and disclosed by Searchlight Cyber analysts Adam Kues and Shubham Shahflaw.
The flaw stems from an authentication bypass in Oracle Identity Manager’s REST APIs, where a security filter can be tricked into treating protected endpoints as publicly accessible by appending parameters like?WSDL or ;.wadl to URLpaths.

#artificialintelligence
Agentic AI is a form of artificial intelligence that does more than just generate; it will act, reason somewhat, collaborate, and execute on its own. Agentic AI transforms its role from a limited tool to that of a collaborative coworker.
This shift affects various sectors, including cybersecurity, national defense, healthcare, key infrastructure, finance, supply chains, and corporate automation. Additionally, it accelerates the integration of robotics, neuromorphic systems, sensor-driven edge computing, and artificial intelligence.
Systems with the ability to plan and pursue goals characterize Agentic AI. IIt combines APIs and tools, engages with dynamic environments, makes decisions, uses reasoning, and continues to learn and adapt.



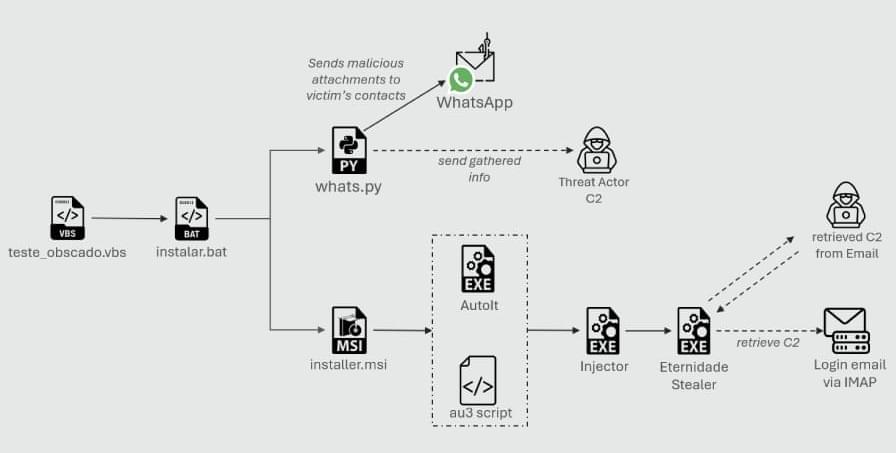
Cybersecurity researchers have disclosed details of a new campaign that leverages a combination of social engineering and WhatsApp hijacking to distribute a Delphi-based banking trojan named Eternidade Stealer as part of attacks targeting users in Brazil.
“It uses Internet Message Access Protocol (IMAP) to dynamically retrieve command-and-control (C2) addresses, allowing the threat actor to update its C2 server,” Trustwave SpiderLabs researchers Nathaniel Morales, John Basmayor, and Nikita Kazymirskyi said in a technical breakdown of the campaign shared with The Hacker News.
It is distributed through a WhatsApp worm campaign, with the actor now deploying a Python script, a shift from previous PowerShell-based scripts to hijack WhatsApp and spread malicious attachments.