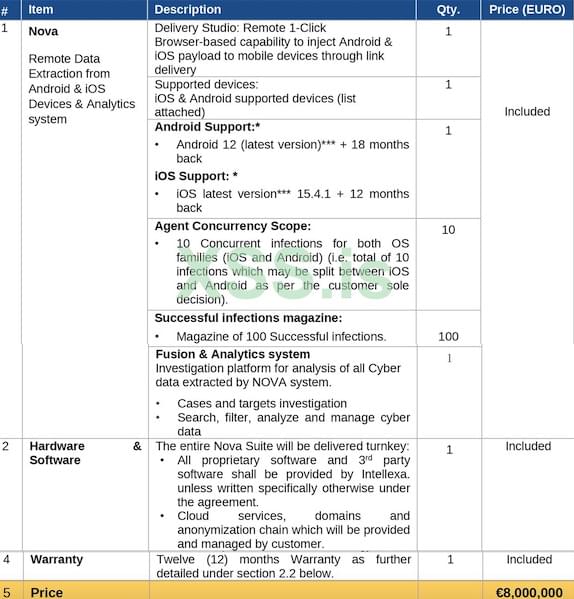
Aug 31, 2022
Leaked Docs Show Spyware Firm Offering iOS, Android Hacking Services for $8 Million
Posted by Saúl Morales Rodriguéz in categories: cybercrime/malcode, law enforcement, robotics/AI
Leaked documents appear to show a little-known spyware company offering services that include Android and iOS device exploits for €8 million (roughly $8 million).
Exploit brokers and mercenary spyware providers have been in the spotlight recently, mainly due to revelations surrounding the use of the controversial Pegasus solution of Israeli company NSO Group.
One of NSO’s fairly new competitors is Intellexa, a company founded by Israeli entrepreneur Tal Dilian. The company claims on its website that it’s offering technologies that empower law enforcement and intelligence agencies to ‘help protect communities’. The company says it’s based in the EU and regulated, with six sites and R&D labs in Europe.