Apr 26, 2023
Google releases security LLM at RSAC to rival Microsoft’s GPT-4-based copilot
Posted by Kelvin Dafiaghor in categories: cybercrime/malcode, robotics/AI
Join top executives in San Francisco on July 11–12, to hear how leaders are integrating and optimizing AI investments for success. Learn More
Today in the Moscone Center, San Francisco, at RSA Conference 2023 (RSAC), Google Cloud announced Google Cloud Security AI Workbench, a security platform powered by Sec-PaLM, a large language model (LLM) designed specifically for cybersecurity use cases.
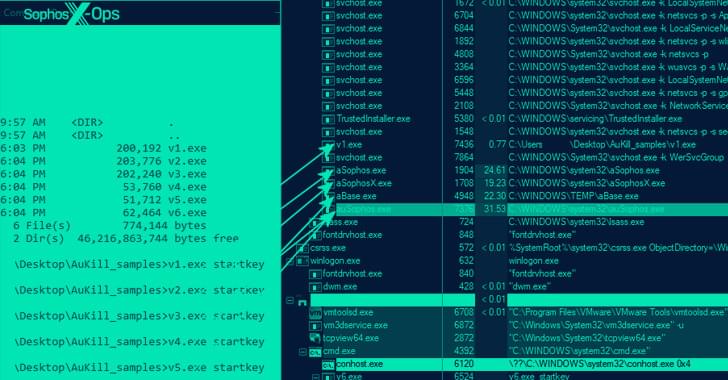
Sec-PaLM modifies the organization’s existing PaLM model and processes Google’s proprietary threat intelligence data alongside Mandiant’s frontline intelligence to help identify and contain malicious activity, and coordinate response actions.