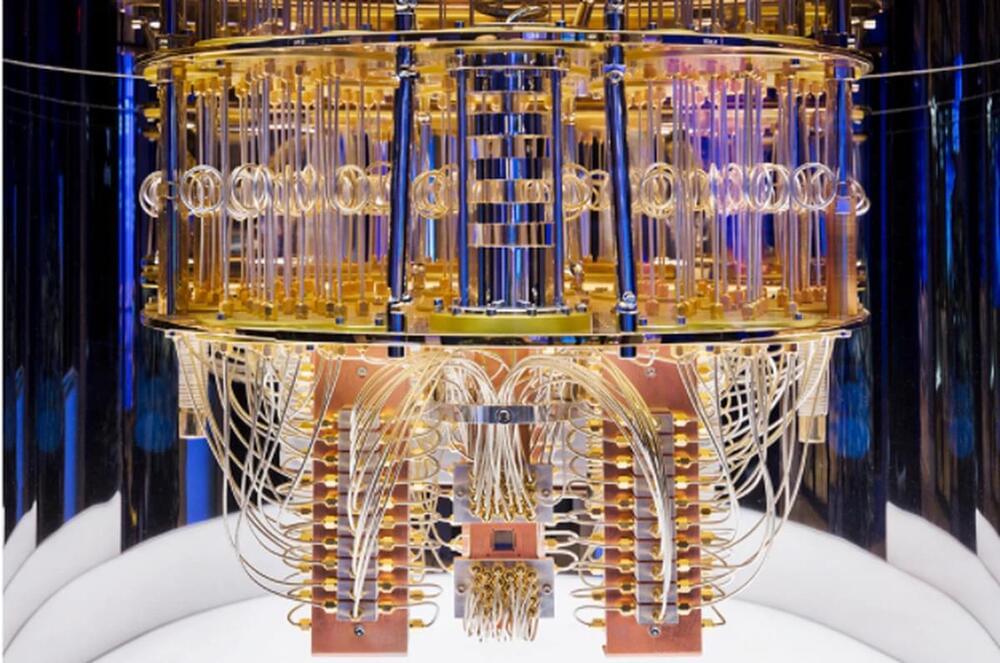
Renting space and IP addresses on a public server has become standard business practice, but according to a team of Penn State computer scientists, current industry practices can lead to “cloud squatting,” which can create a security risk, endangering sensitive customer and organization data intended to remain private.
Cloud squatting occurs when a company, such as your bank, leases space and IP addresses—unique addresses that identify individual computers or computer networks—on a public server, uses them, and then releases the space and addresses back to the public server company, a standard pattern seen every day. The public server company, such as Amazon, Google, or Microsoft, then assigns the same addresses to a second company. If this second company is a bad actor, it can receive information coming into the address intended for the original company—for example, when you as a customer unknowingly use an outdated link when interacting with your bank—and use it to its advantage—cloud squatting.
“There are two advantages to leasing server space,” said Eric Pauley, doctoral candidate in computer science and engineering. “One is a cost advantage, saving on equipment and management. The other is scalability. Leasing server space offers an unlimited pool of computing resources so, as workload changes, companies can quickly adapt.” As a result, the use of clouds has grown exponentially, meaning almost every website a user visits takes advantage of cloud computing.