Nov 3, 2022
Researchers discover security loophole allowing attackers to use Wi-Fi to see through walls
Posted by Jose Ruben Rodriguez Fuentes in categories: drones, internet, security
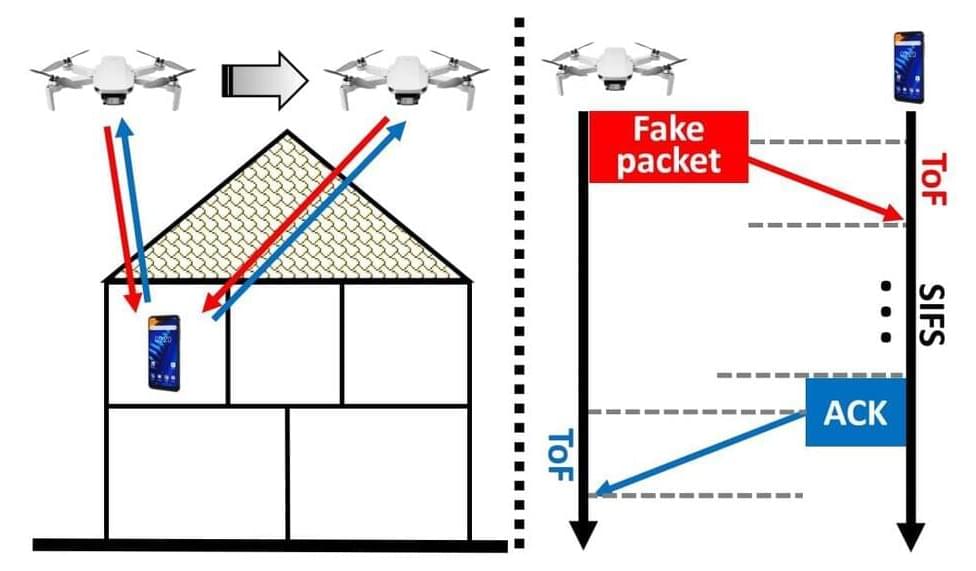
A research team based out of the University of Waterloo has developed a drone-powered device that can use Wi-Fi networks to see through walls.
The device, nicknamed Wi-Peep, can fly near a building and then use the inhabitants’ Wi-Fi network to identify and locate all Wi-Fi-enabled devices inside in a matter of seconds.
The Wi-Peep exploits a loophole the researchers call polite Wi-Fi. Even if a network is password protected, smart devices will automatically respond to contact attempts from any device within range. The Wi-Peep sends several messages to a device as it flies and then measures the response time on each, enabling it to identify the device’s location to within a meter.